Deep IS – "Counterfeit protection technology"
Pressure Sensitive Labels/ Security systemProtecting brand value with anti-counterfeiting technology.

'Deep IS' is a trademark or registered trademark of the Fuji Seal Group.
Deep IS promotional video
What is "Deep IS, image identification technology"?
"Deep IS, image identification technology" was developed by FSG together with the Swiss start-up DynamicElement, aiming to ensure an anti-counterfeiting and traceability system to protect product value and brands.
"Deep IS" is a security system that detects subtle fluctuations which naturally occur in printing.
Advantages of Deep-IS
- No special processing required
- Can be applied to existing label designs without requiring special printing, materials or components.
- Stealth identifier
- Stealth security operation is possible.
Third parties can not detect the security identifier, as it uses features of the printing as an identifier.
- Verification via smartphone
- Smartphones can be used for verification.
*There are limitations to applicable smartphone models, please contact us for details.
- Traceability
- As a digital fingerprint is generated for each label individually, the identifier will not match even in cases where the label is copied. Traceability application is possible based on the individual identification information.
*Please refer to [On traceability application] for further details.
About the Image Identification Technology
- Technology
- Using an algorithm, the system makes the individual identification of the verified image by comparing a portion of the printed design and the registered image.
The individual identification is verified by the naturally occurring features in printing that cannot be distinguished by the human eye.
- Features
-
- (1)Fine-grained identificationSmall areas are broken down and given identifiers.
- (2)Dirt and scratch resistantDurable and resistant to external factors such as friction.
- (3)Compatible with any label design*Existing designs can be used without modifications.
- (4)Identifier which can not be easily detectedThird parties can not detect the security identifier.
*Prior verification is required as some restrictions such as sufficient printed area within the image, no reflection due to holograms, vacuum metalized coating, etc. may apply.
Proposed method of operation (for anti-counterfeiting)
- Design Setup
- The design is setup as desired by the customer.
- Producing Deep IS label
- When the label is manufactured, the images of the design as agreed with the customer are registered in the individual identification number.
- Customer
- The customer attaches the label with the registered individual identification number.
*No additional steps required.
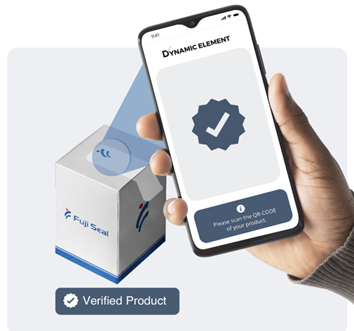
- Verification
- Verification is possible via a smartphone application.
About the Traceability Application
*We are also continuing to develop this traceability system. Please contact us for further the details.
Application example (QR code two-factor authentication)
- Issue
- QR codes, which are widely used in general, can be easily copied.
- Proposal
- The surface of the QR Code is individually identified to realize a two-factor application of the QR Code.
- Primary factor:Uses the QR Code as usual
- Secondary factor:Verifies of the surface of the registered QR code to determine its authenticity.
- Note
- Conventional QR Codes can be used for management and marketing (primary factor), while "Deep IS" can be used for security functions (secondary factor).

Industry
Deep IS Service Materials
Deep IS Service Request & Inquiry

Please contact to us via our Web site to get more detail info.




